Death, taxes, and terrorism. A motto for the 21st Century, perhaps? Terrorist activities permeate almost every corner of our society. Be that through horrific attacks, or the development of international security policies, terrorism influences the decisions and day-to-day living of billions of people.
The early 21st Century is remarkable for many things. The continued rise of social media is certainly one of them. Of the estimated 7.4 billion global inhabitants, 2.3 billion are social media users. That's over 31%.
Consequently, social media networks present a powerful tool to terrorist groups. The instant reach and potential viewership in the billions, combined with little genuine consequence for those uploading atrocities, or using them as a recruitment tool, means social media networks will continue to be abused.
Critical Infrastructure
Social media has undoubtedly transformed terrorist groups' ability to distribute media across the globe. The robust online presence demands a constant stream of potential viewers. Social media networks make the dissemination of information incredibly easy, as well as providing an excellent recruitment network.
Social media networks such as Twitter and Facebook have been paramount to this illusion of media control. They offer unlimited traffic, a global audience, and little fear of digital reprisal. Terrorist groups' continued exploitation of social media has understandably seen some platforms pushback.
Twitter Leads the Way
Most notably, Twitter take an extremely aggressive stance toward any pro-ISIS accounts. In July 2015, Twitter received an extremely public dressing-down from current FBI Director James Comey.
ISIL is reaching out, primarily through Twitter, to about 21,000 English-language followers. It buzzes in their pocket ... a device, almost a devil on their shoulder, all day long saying, "Kill, kill, kill, kill."
Comey also noted that ISIS recruitment strategy is vastly different to other terrorist groups. Instead of funding spectacular, attention grabbing attacks against Western landmarks, ISIS encourage people to travel to the so-called caliphate.
Twitter received the message, loud and clear.
Twitter suspended over 125,000 accounts between Director Comey's reprimand and their February 2016 announcement. Since then, Twitter has ramped up its efforts, suspending a further "235,000 accounts for violating our policies related to promotion of terrorism." As a result, all Daesh (a supposedly derogatory term for ISIS) traffic on Twitter has dropped by 45% in two years.
Prominent pro-ISIS (unofficial) media wing al-Battar rebuked the terrorist groups' social media supporters:
Why have you migrated from the battlefield of Twitter and Facebook and entrenched on Telegram? Maybe you don't know or didn't notice the difference between Telegram, Twitter, and Facebook, which is a big and significant difference.
A clear response to strategy reaping rewards.
Facebook Fighting Back, Too
A different social media, a different strategy. In fact, due to the scale of Facebook, the social network implements a number of anti-terrorist strategies.
One strategy involves identifying teenagers and young adults who post content containing terms such as "sharia" or "mujahedeen." Once identified, they began to see a series of animated videos on their Facebook news feed, with some videos containing cartoon figures posing underneath an Islamic State flag. A narrator says "Do not be confused by what extremists say, that you must reject the new world. You don't need to pick. Remember, peace up. Extremist thinking out."
Experimenting with strategy appears to be reaping dividends. Alphabet -- Google's parent company -- funded three experimental advertising projects designed to counterbalance extremists use of both Twitter and Facebook.
Alphabet contributed an undisclosed amount of money to the projects. As a result, U.S.-based non-profit Average Mohammed made animated videos that explain Islam while criticizing terrorist groups. Harakat-ut-Taleem, who are run by an anonymous group in Pakistan, made videos dissuading people from joining the Taliban. ExitUSA created a series of videos targeting white supremacists, with a focus on those already radicalized.
Message Branding
ISIS and other terrorist organizations seek to exploit social media as a propaganda dissemination tool. In a nod to modern businesses, ISIS understand that branding makes a huge difference. Terrorist recruitment networks target individuals on the cusp of society that can be further disenfranchised. Consequently, messages of positive support and inclusion coming directly from the government might be met with immediate disdain (Paywall):
Once the message is stamped "government," for many young people, it's tainted.
Furthermore, messages carrying logos or other officialdom may further cement anti-government rhetoric, and can be played upon by those recruiters.
Facebook added to their counter-terrorism tactics by allowing former members of terrorist groups to create fake accounts. The fake accounts were then used to send positive messages to extremist groups known to be active on the social media network. The friendlier tone, coupled with the lack of direct government interjection resulted in longer lasting conversations.
The Redirect Method
Alphabet realize the power of search -- understandably!
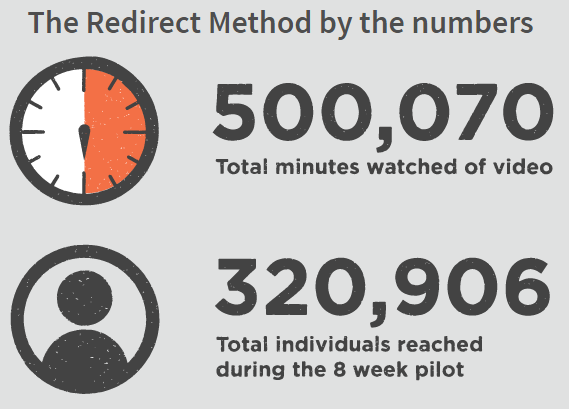
Over the past year Google has worked with tech incubator and think tank, Jigsaw, on an innovative advertising program known as the Redirect Method. Its premise is simple, but brilliant: combine the power of Google's advertising algorithm and YouTube's video network to beam targeted adverts at users searching for terrorist or jihadist related terms.
Jigsaw ran a surprisingly successful pilot program earlier this year. During the two-month trial over 300,000 people clicked through to the anti-ISIS YouTube channel. Furthermore, Jigsaw found those who clicked through spent more than twice as long viewing the channel than the best estimates of how long people usually view YouTube.
Whack-a-Mole
Unfortunately, the sheer range of social media networks and social messaging apps has created an almost impossible task. I'm not sure if it is more akin to digital whack-a-mole, or slaying the Lernaean Hydra, but according to Susan Benesch, a faculty associate at Harvard University's Berkman Klein Center, "It's simply impossible to remove it all. Even if one platform successfully takes something down, usually that content is available somewhere else."
In the case of ISIS, this is clearly what has happened. While Twitter may have reduced their ISIS related content by 45%, encrypted messaging service Telegram reports an enormous surge in terrorist related activities:
One jihadist group, known as Horizons, runs two channels on Telegram, an encrypted communication platform. These channels exist primarily to educate supporters on how to leverage technology to further the jihadist agenda.
Spotting terrorist related activity is a difficult proposition, too. Twitter, Facebook, and other social media networks point to advanced algorithms that can spot recurring patterns in files containing child abuse. YouTube use a similar process to identify videos that breach copyright. However, there isn't a set image, file, video, or audio track that defines terrorist or extremist activity. Not to mention that terrorist groups are adaptive, altering their behavior as to remain undetected.
All-Seeing Eye
Social media networks do wield considerable power. Some would argue their unique position as global communication mediators means they assume a position of responsibility. There are certainly people who believe the all-seeing eyes of social media can perform some sort of magical technological spell to pinpoint each and every terrorist around the globe.
That simply isn't true. Regardless, we see social media networks, and the world's largest online search provider working together to provide viable anti-terrorist strategies. As much as people want it to be a cure-all, and as amazing as that would be, our reality isn't as simple.
Social media networks have introduced some interesting strategies. What do you think they could do? Do you have any anti-terrorist strategies for social media? Let us know your thoughts below!