New Year's Day has long gone, but it's not too late to make a positive resolution for the upcoming year.
I'm not talking about eating well, or drinking less caffeine, although you'd be well advised to do so. Instead, I'm talking about taking steps to safeguard your online security and privacy in the year ahead. Here's how.
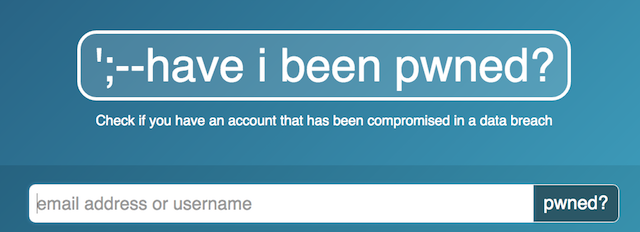
Find Out If Your Have Been "Pwned"
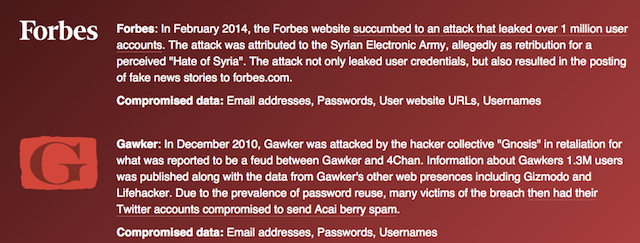
As the name suggests, HaveIBeenPwned.com tells you whether your personal details have been splashed across PasteBin, or otherwise leaked to the Internet. It's a great way to see if you've been caught up in a data breach. Their database includes high-profile leaks from Adobe, Comcast, Ashley Madison (obviously), and much more.
You don't need to register. Just type in your email address or username, and it'll let you know what sites have leaked your data, when it happened, and more importantly, what was leaked.
You can also subscribe to get notifications should your email and username appears in any future breaches.
If you're unfortunate enough to have been caught up in a leak, your best bet would be to take proactive steps to mitigate the damage. If a site has leaked your passwords, and they failed to hash and salt them, change that password wherever you might have used it.
If more dangerous stuff has been leaked, such as your name, address and biographical data, you might want to invest in some online credit monitoring.
Sort Out Your Social Media Privacy Settings
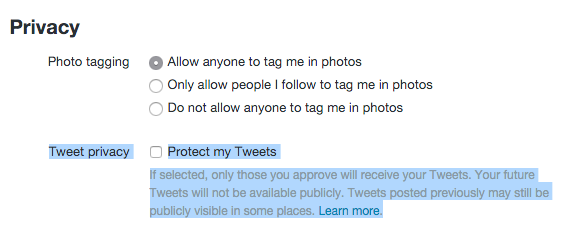
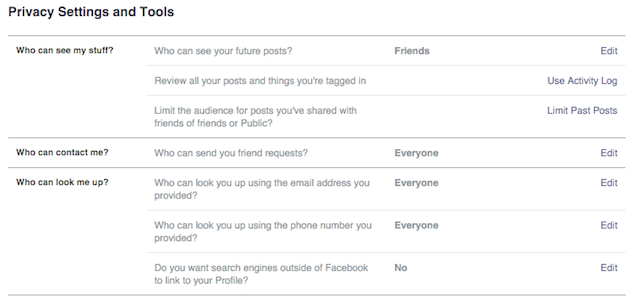
Most of us are on Facebook and Twitter. They're both near-ubiquitous. But very few of us are preoccupied with what our privacy settings look like. We just set them once, and forget about it. This February, try and revisit them to see if they're still what you want.
You can change your Twitter profile to private by clicking on Settings, Privacy, and under Tweet Privacy, check the box that says Protect My Tweets.
On Facebook, click Settings, and then Privacy. Then you can refine your settings as you wish. You can also use Facebook's free Privacy Checkup tool.
Make this the year you experiment with a new, privacy-focused social network or messaging. Ello was an abject failure, and App.net is long-dead, but there are other services you can use which are really good. Right now, I'm playing around with Sessme.
Available for Android and iOS, this service allows you to have a greater control over the messages you send. Sessme allows you to remotely delete or encrypt the messages you send (which is handy if you accidentally send an embarrassing message to your grandmother or boss). And of course, everything you send is encrypted, so it can't be intercepted in transit.
Get Into The Habit of Disposing of Mail Properly
Junk mail is annoying. I'm constantly being bombarded by adverts for magazines, credit cards, and first-time mortgages. I don't want them. But I also don't want to be the victim of identity fraud.
Which is why I always make the effort to securely destroy any junk mail I get. I ensure that before it enters my bin, I first shred anything that contains my personal information.
This goes double for letters from my bank and credit card company which I no longer require.
By destroying junk mail, you ensure that nobody can obtain your personal information through dumpster diving. If you're not sure what types of mail and documents you should destroy, check out this piece from fellow MakeUseOf security writer, Philip Bates.
Get Informed About Security and Privacy Threats
Scammers and hackers depend totally on their victim being blissfully unaware they're being scammed and hacked.
Tech support scams only work when the victim doesn't know it's not actually Microsoft on the other end of the line. People only pay for fake anti-malware when they don't know it's utterly ineffectual, and was installed on their machine through false pretenses. People only click on phishing emails when they don't know what to look for.
Which is why you should always make the effort to learn about the security threats you might face.
We regularly write about security issues on MakeUseOf. But there are a number of other security blogs, who will do an equally good job of keeping you informed. One of my favorites is the Sophos Naked Security Blog.
If you're a fan of Twitter, we have also recommended some security experts you absolutely should follow.
Finally, if YouTubers are more your thing, you should totally subscribe to J4VV4D. He walks that line between being informative, and being side-achingly funny.
By ensuring that you're constantly learning about the evolving threats to your security and privacy, you go a long way to protecting yourself.
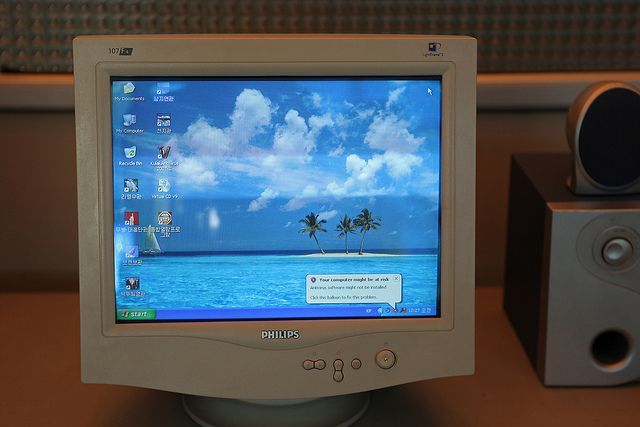
Finally Update Those Virus Definitions and Run A Scan
"Warning: Your Definitions Are Out Of Date. Last updated 398 days ago." Click
It's a paradox. Your antivirus program wants you to update your definitions, so it bugs you with notifications that are hard to dismiss, and seldom gel with the Windows aesthetic. It's almost like you're still using Windows XP.
They're so annoying, you ignore the dire warnings that your antivirus is telling you. Eventually you find the setting that tells it to permanently shut up, and you switch it on. Problem solved, right?
Look. I know that most AV programs are ugly and badly designed. I know they're annoying, and their warnings can get in the way of whatever it is you're doing. But at the risk of sounding like your mom, it's for your own good.
If your definitions are out of date, then you have no protections against any viruses that have came out since you ran the updates. Many malware programs, in order to prevent being removed, will try to prevent your machine from downloading updates once infected. It is for this reason why you should run updates while your computer is in a good condition.
So, please. For me. Run your updates, and do a scan while you're at it.
Commit To Being Proactive About Your Digital Security
New Year's resolutions are all the same. You say you're going to do a particular thing, and have a committed effort for about a month where you do that thing. Then February arrives, and - no surprises - you stop doing that thing.
But this? This should be different, because it directly pertains to your own privacy and security. In the months ahead, you should commit to being proactive about keeping your machine secure, and by practicing good data hygiene.
Not only should you be running regular malware scans, but you should try and ensure that your system is regularly updated and patched. If you're still on Windows XP, make this the year you move to something more current.
You should also make the effort of ensuring all the software you use is current, too. Whenever you see a pop-up for a Java update, download it. That goes double for Adobe Reader, Flash, and Microsoft Office.
Don't Be Afraid of Starting Afresh
Finally, if your computer is a slow, malware-encrusted slag-heap of a machine, don't be afraid to start from afresh. Windows 8.1 and Windows 10 both allow you to restore your machine to factory settings.
I follow this rule: If I'm not confident with typing my credit card number on my computer, I wipe it. So should you.
Have a Secure and Private Year
By following these simple rules, you can drastically reduce the threats to you from outside sources, and safeguard your privacy.
Have you got your own strategies for staying secure this year? Any resolutions you're following? Let me know in the comments below.
Photo Credit: Stethoscope on laptop by Twinsterphoto via Shutterstock, Antivirus (Roman Harak)