In the wake of the Edward Snowden leaks, the National Security Agency (NSA) is turning to cloud storage for their data. Why? Isn't that counter-productive? And how secure are the clouds you use?
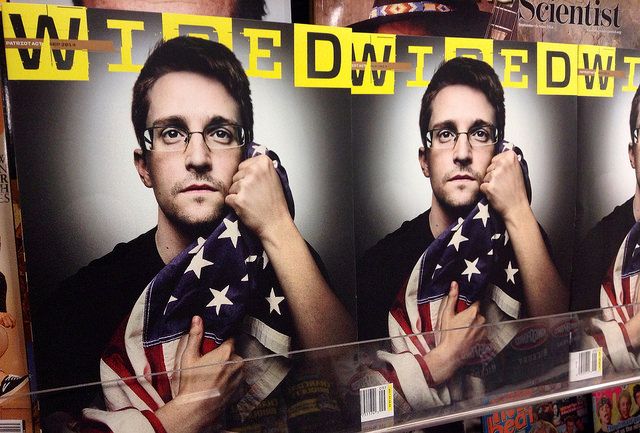
Edward Snowden, a former contractor at the NSA, leaked files revealing the full extent of surveillance operations worldwide, forcing numerous serious discussions on our privacy and security.
For the NSA, it had major impacts: not only are people questioning how and why they're being spied on, but the NSA Director, Michael Rogers, admits the leaks considerably hampered intelligence gathering.
The agency is taking unexpected steps to stop another leak: they're putting all their data in one place.
What Are They Actually Doing?
After expansions in their authorities, the amount of data collected by intelligence services expanded, namely covering smartphone metadata. Largely stored on servers, much of this data was revealed by Snowden across 2013 and 2014, most notably PRISM.
But the whistleblower isn't the sole reason the NSA are turning to the cloud.
The agency began adopting centralised storage in 2010 in a bid to share information across the United States Intelligence Community (IC). Their clouding system of choice? Amazon Web Services, which links the 17 elements of the IC, including the Central Intelligence Agency (CIA), Federal Bureau of Investigation (FBI), and Office of Naval Intelligence (ONI). As well as its increased capacity, the service boasts speed and cost-effectiveness. Jon Koomey, an energy futurist, told National Geographic:
"When you step into the cloud and replace atoms with bytes, you don't have to manufacture chips anymore - and that means big savings."
Data is metatagged for accessibility and accountability: these detail personnel with access to said information, so their actions are all logged. This is paired with compliance regulations, so only those legally authorized to see material can do so.
The NSA's current cloud consists of two systems: an internal one used by agency employees; and the GovCloud, available across the IC via the Joint Worldwide Intelligence Communications System. Essentially, in the latter, the NSA acts as a service provider to other IC sectors.
Both clouds are set to merge by the end of this year, but full transition will take years to complete.
How Secure Is It?
Much of the wealth of data is currently being stored at, and is accessible through, the Utah Data Centre, a $1.5 billion hub between Great Salt Lake and Utah Lake. The facility was completed last month after power surges damaged equipment causing a year-long delay, and houses servers across four 25,000-square-foot halls.
The NSA admits to collecting Internet searches, phone calls, financial data, and health records, and analysts plough these for operational applications.
The building itself is heavily fortified: obviously only authorized personnel gain entrance through the control centre, and security guards patrol the hub. They're assisted by CCTV, intruder detectors, and further protection costing over $10 million. Rory Carroll writes:
"A small exit – not marked on ordinary maps – takes you up a curving road. A yellow sign says this is military property closed to unauthorised personnel.
Further up the hill, invisible from the highway, you encounter concrete walls, a security boom and checkpoint with guards, sniffer dogs and cameras. Two plaques with official seals announce the presence of the office of the director of national intelligence and the National Security Agency."
The complex might be sound, but how secure is the actual cloud?
Former director of the NSA, General Keith Alexander says the strict legal structures to ensure compliance also protect civil liberties, so data that needs to be deleted in a set time limit automatically notifies staff when that period is up.
This accountability is total. Content and personnel are tagged at a cellular level, meaning full records of everyone who has accessed, copied, printed, or altered files – or even single words and names. This is partly enabled using the public-key infrastructure (PKI), whereby data is encrypted and decrypted with public and private key pairs, and identities are verified by the Certificate Authority (CA). These records are kept on a Certificate Database, Store, and Key Archival Server, and further safeguards against corruption during transit.
Additional security methods understandably have to be kept secret, but Alexander explains:
"[W]e do utilize a variety of security protocols at every layer of the architecture, as well as a robust encryption strategy. The NSA cloud brings together multiple data sets and protects each piece of data through security and enforcement of the authorities that specify its use... In addition to data markings, security is applied throughout the architecture at multiple layers to protect data, systems, and usage."
How Safe Are The Clouds You Use?
We use cloud computing systems for storage and sharing (think DropBox, Apple's iCloud, or GoogleDrive), emailing, and for eCommerce. But this is important to remember: these clouds are different to the one used by the NSA. They've got to be. National security secrets are generally considered more important to keep hush-hush than a vast array of selfies uploaded to the iCloud.
Nonetheless, your information isn't exposed for all to see. The core security measures are: preventative (the first line of defence - two-step ID verification, for example); and deterrent (emphasis on consequences for potential hackers); while detective (architectural monitoring) works hand-in-hand with corrective controls (or damage limitation).
Your data may be stored on a different company's server, but it's not all about location; instead, it's how it's accessed. Solid data encryption is essential, yet far from the only way firms need to secure your information. Compliance data, similar to the NSA's but certainly not as thorough, could also be employed so details can only be accessed under certain contexts, or identify a breach by auditing applications for unusual activity.
Of course, this isn't absolute. Apple faced a potentially massive issue last year when the accounts of several celebrities were hacked and compromising photos leaked. Apple, however, doesn't see this as their fault, but regardless have increased their security.
Interestingly, Lucas Mearian argues that clouds aren't secure – at least not from service providers, and government departments like the NSA. Combine this with the NSA's claim that they want a "front-door" to your data via split-key encryption and your data might be safe from hackers, but not from intelligence agencies.
Do You Trust The Cloud?
Cloud computing isn't perfect, but it certainly has its advantages.
The NSA has adopted it as a cost-cutting measure, sure, but the large-scale accountability is their effort to combat another Snowden-esque leak, acting as preventative, deterrent, and detection controls.
And if you're still concerned about the security of the clouds you use, you're not powerless. You can secure your DropBox account, create your own cloud using the open-source Seafile – or even explore more encryption methods.
The NSA thinks the cloud is the future. Do you?
Image Credits: Secure Cloud Computing by FutUndBeidl; Snowden on Wired Cover by Mike Mozart; and System Lock by Yuri Samoilov.