NFC (Near Field Communication) payments are becoming increasingly mainstream. Although the United States has been a bit slow on the uptake, people in the United Kingdom have been using the technology since 2011. In more recent years, NFC payments have also exploded in popularity across Europe, Canada, and Australia.
One of the biggest selling points of NFC payments is better security. We've spoken at length about the security features offered by Apple Pay elsewhere on the site.
But don't be fooled. NFC contactless payments don't provide a cast iron guarantee of safety. Just like any financial transaction, there are weaknesses and loopholes.
Here are five NFC security issues you need to consider before you make your next contactless payment.
1. Eavesdropping
Eavesdropping is arguably the number one threat facing all NFC contactless payments. The term refers to a criminal "listening in" on an NFC transaction.
Unlike handing over cash in a store, the nature of NFC payments means the payment device and the terminal are transmitting electronic data. That data can be used by thieves to ascertain private information about the user. It could take the form of bank details, but also information needed for simple identity theft like names and addresses.
Broadly speaking, there are three main aspects to an NFC transaction: air interface signals capture, communication channels decoding, and captured data analysis. It is the first part which is at risk of eavesdropping.
NFC payments use magnetic coupling to manage the energy transference between the HF RFID reader and tag antennas. The coupling places limits on how far signals can reach, but some white hat hackers claim they've succeeded from as far away as five meters.
Ultimately, if an interceptor can receive, amplify, process, and decode the leaked signals, they can eavesdrop.
Solution: Only use secure channels to make payments. Secure channels encrypt data so only an authorized device can decode it.
2. Are You Using an Up-to-Date App?
NFC contactless payments are made possible by apps. The NFC technology is hardware within your phone or tablet, but it's the individual app or operating system that decides how the technology is used.
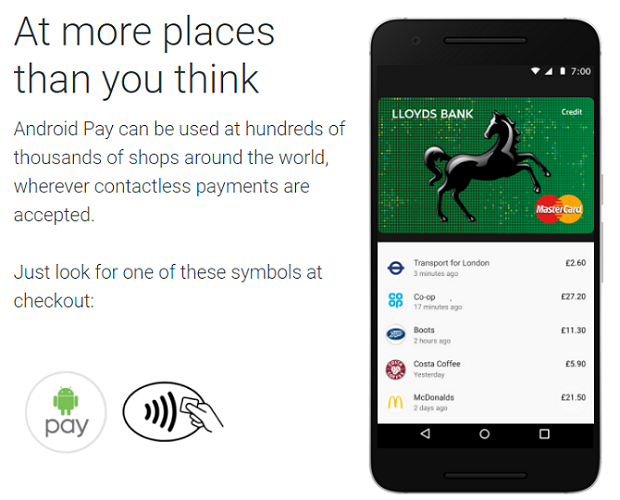
Even if you don't use NFC payments, you're probably familiar with some of the leading players in the sector. They include Samsung Pay, Apple Pay, Android Pay, LifeLock Wallet, and Square Wallet. Several bank apps also have the feature.
Like any app on your phone, you need to update these apps frequently. Obviously, an up-to-date app will give you access to the latest features, but it will also ensure you're using the version of the app with the most recent security fixes.
If you're not running the latest version of an app, you could be putting your financial security in jeopardy.
Solution: Always make sure you have automatic updates enabled on your device.
3. Theft
Last year, almost 2.5 million Americans had their smartphones stolen. Historically, if you were the victim of a theft, it was annoying but not life-changing. If you were diligent, your contacts, photos, messages, and other valuable data would have been in the cloud -- you didn't lose anything.
However, with the growing prevalence of NFC contactless payment apps, that could be about change.
Of course, if you take your mobile security seriously, you generally shouldn't have anything to worry about. Your phone and payment app will be protected using passwords, PINs, and biometrics.
However, thousands of people don't take these precautions. They're vulnerable. You might also be vulnerable if you disable PIN prompts for set periods of time after a transaction, then lose your phone during that time period.
But ignoring lax user security and unfortunate sequences of events, is there still a risk? Yes, but it's minimal. The way the payment apps use tokenization prevents them from working if they detect a hacked PIN code.
Solution: Don't take shortcuts with your phone's security. Always enable all the available protections at both the device and app level. If you lose your phone, immediately contact your bank and your wallet app provider.
4. Interception Attacks
Let's return to some technical insight. In addition to eavesdropping attacks, you're also vulnerable to interception attacks. They function in a similar way to man-in-the-middle attacks: a hacker receives information from one device, alters it, then passes it to the intended recipient.
With NFC, the risk is negligible, but it exists. Hackers can only make it work if the two devices are both in Active mode. If one is in Passive mode, the two devices cannot receive and send information at the same time.
Even if both are in Active mode, the devices could recognize a protocol error and stop the transmission.
The bottom line is interception attacks are hard to operate, but not impossible.
Solution: Leave NFC turned off whenever you're not using it. When it's enabled, leave your device in Passive mode to prevent an accidental Active-Active pairing.
5. Consumer Privacy
You didn't think we'd be able to make it through the whole article without discussing privacy, did you?!
It should come as no surprise that NFC payments are going to bring a host of new privacy issues to the fore over the coming years.
To understand the current situation, it's necessary to explain some background. In 1999, the United States Congress passed the Gramm–Leach–Bliley Act (GLBA). One of the many changes it implemented was to make mobile payment service providers akin to financial institutions and allow their consumers to opt out of sharing personal information for third-party marketing.
The decree was followed up in 2003 by the CAN-SPAM Act (CSA) and the Telephone Consumer Protection Act (TCPA). The Acts made it illegal for companies to send unsolicited commercial emails and text messages to wireless devices. But crucially, the Acts do not apply when a person has established business relationship with the would-be sender.
So far, so good. However, GLBA, CSA, and TCPA are not suitable for the modern era of NFC payments.
Although nobody has yet tested it in the courts, it seems GLBA will not apply if either a consumer or an app (rather than a financial institution) discloses the information to shops and vendors during an NFC transaction.
Similarly, CSA and TCPA won't apply. By paying a vendor, you have established a business relationship with it.
There are a few likely outcomes of these loopholes:
- We can expect more shops to upload ads, coupons, and even adware onto our devices during an NFC transaction.
- We might start seeing other providers using information about our purchases to show us targeted ads across the web.
- We will probably start seeing software licensing agreements and point-of-sale notices forcing us to give consent for receiving marketing messages.
Solution: Read the small print of an app, read a shop's terms of business, and always delve into your wallet's settings to see if there's a way to prevent data transfers of this nature.
Does NFC Security Worry You?
As this article has demonstrated, NFC is far from being a magic bullet that will instantly solve all the insecurities in the financial industry. You're at risk from technical issues, practical issues, and privacy issues.
However, NFC is probably still safer than using the old magnetic strip-based bank cards or even the more recent innovations of Chip-and-PIN.
Do you use NFC contactless payments? Does the security of the payments worry you? Have you been the victim of an NFC crime? As always, you can leave all your opinions and thoughts in the comments section below.
Image Credit: Wavebreakmedia/Depositphotos