When we talk about security and privacy, there are several considerations. One of the biggest is whether the software you're using to access the internet is safe or not. By extension, you might also want to consider how the websites you visit use your information.Three tools come to mind when you consider addressing these issues: the privacy and anonymity-focused Tor browser and network, the Invisible Internet Project (I2P), and the most commonly known, a VPN.But how do these online privacy tools work, and which should you use to protect your privacy online?
Tor
The "Tor" name derives from the original software project name: The Onion Router. Tor software directs web traffic through a worldwide system of interconnected relay nodes. This is known as "onion routing" because your data passes through many layers, and websites on the Tor network are known as onion sites.
In addition to the layers, Tor encrypts all network traffic, including the next node IP address. Encrypted data passes through multiple randomly selected relays, with only a single layer containing the IP address for the following node decrypted during transit.
The final relay node decrypts the entire package, sending the data to its final destination without revealing a source IP address at any point.
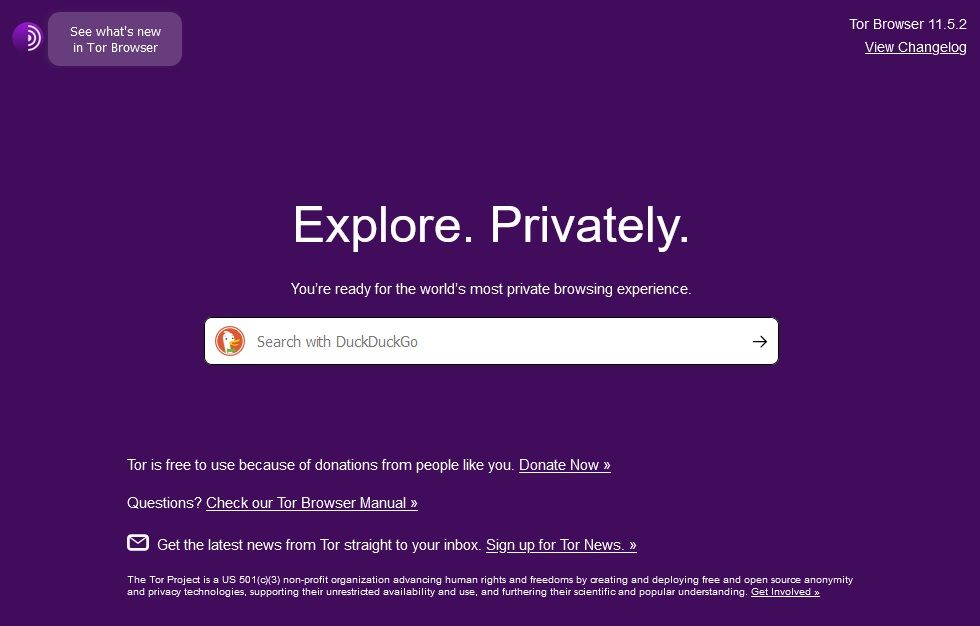
How Do You Use Tor?
The Tor Browser is the easiest way to use Tor software. Download and install the browser as you would any other piece of software. The setup will continue after you open Tor Browser for the first time. Then you browse as normal. It will be slightly slower than normal—sending the data through multiple relays takes time. Tor isn't the same as other browsers with built-in privacy features; it's a whole network.
Why Should You Use Tor?
The Tor Browser encrypts all data transmissions. As such, a huge range of people use it: criminals, journalists, hackers/crackers, law enforcement (to protect communications and solve crimes), government agencies, and much more. In fact, Tor started life as a U.S. Naval Research and DARPA project.
The Tor Browser is also one of the most direct routes to the dark web (not to be confused with the deep web). The dark web is the so-called "dark underbelly" of the regular (sometimes referred to as "surface") web that we browse daily. Whenever you hear a story about an online marketplace selling illicit substances and goods, they're talking about a site hosted on the dark net.
But Tor isn't just about crazy secret marketplaces and secret communications. You can use it for other "normal" things like browsing Facebook. For instance, airlines use complicated algorithms to keep tabs on interest in their flights, adjusting price with demand. Keep visiting the same site, using the same IP, and the airline knows you're interested—but the price usually increases. Check the same flights using the Tor Browser, and you can find some interesting discounts.
Will Tor Protect Your Privacy?
Yes, for the vast majority of users. The Tor design protects privacy from bottom to top. If you're just using Tor Browser to browse the dark web, you're not going to alert anyone. However, many privacy advocates consider the Tor network compromised. National Security Agency (NSA) program XKeyscore records everyone who visits the Tor webpage and downloads the Tor Browser. Furthermore, they class those that download and install it as "potential extremists."
So, yeah, sorry, you're on a list now. (They think similarly of those who use Linux, so don't worry too much.)
Tor only encrypts data sent and received within the Tor Browser (or a different browser using Tor software). It does not encrypt network activity for your entire system.
For more on Tor, take a look at ways to stay away from compromised Tor exit nodes.
I2P
The Invisible Internet Project (I2P) is a garlic routing protocol. This is a variant of the onion routing protocol used by Tor.
I2P is an "anonymous overlay network." The garlic routing protocol encrypts multiple messages to make data traffic analysis difficult, while increasing network traffic speed. Garlic routing takes its name from actual garlic. Each message is a "garlic clove," with the entire encrypted bundle representing the "bulb." Each encrypted message has its own specific delivery instruction, and each end-point works as a cryptographic identifier (read one of a pair of public keys).
Each I2P client (router) builds a series of inbound and outbound connection "tunnels"—direct peer-to-peer (P2P) networking. A major difference between I2P and other P2P networks you have used is the individual selection of tunnel length. The tunnel length is a factor in anonymity, latency, and personal throughput and forms part of the individual peer threat model.
The result is that the smallest number of peers possible relay messages according to each peer's sender and receiver threat model.
How Do You Use I2P?
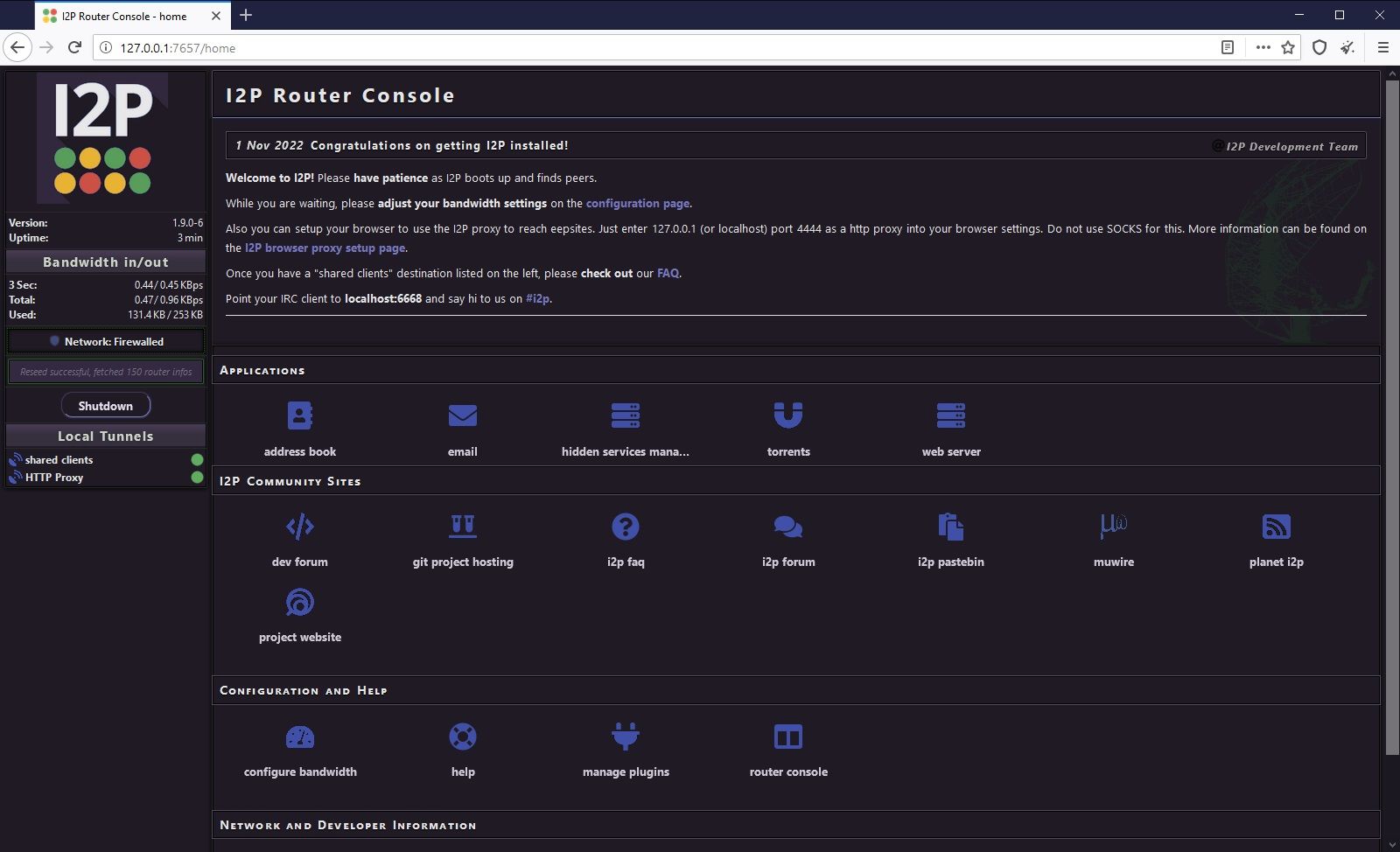
There are now two methods for using I2P.
The first way to use I2P is to download and install the official install package. Once installed, search for and open Start I2P (restartable) in your Start menu. This will open a locally hosted web page, which is the I2P Router Console, or in other words, the virtual router used to maintain your I2P connection. You'll also notice the I2P Service command window—ignore this and leave it running in the background.
The second method is to download and install the newer all-in-one Easy Install Bundle For Windows (Beta), available at the same website as the official installation package. The major difference between the two is that the Easy Install Bundle creates an I2P profile in either Mozilla Firefox or Tor Browser (which is also a version of Firefox) for easy use. After downloading and installing the package, follow the on-screen instructions to complete the Easy Install Bundle configuration, and you'll arrive at the I2P Router Console.
In both cases, the I2P service can take a few minutes to get up and running, especially during the first boot. Take the time to configure your bandwidth settings.
I2P allows users to create and host hidden websites, known as "eepsites." If you want to access an eepsite, you'll need to set your browser to use the specific I2P proxy. The I2P proxy configuration details provide more information, plus additional steps to use I2P with a Chromium-based browser (like Chrome or Microsoft Edge).
Why Should You Use I2P?
I2P and Tor offer similar browsing experiences for the most part. Depending on your I2P bandwidth configuration, it is probably slightly faster than Tor Browser and runs from the comfort of your existing browser. I2P hosts many hidden services, some of which are faster than their Tor-based equivalents, which is a massive plus if you're frustrated with the Tor network. However, the number of I2P services has fallen over the years in comparison to Tor.
I2P runs alongside your regular internet connection, encrypting your browser traffic. However, I2P isn't the best tool for browsing the open web anonymously. The limited number of outproxies (where your traffic re-joins "regular" internet traffic) means it is less anonymous when used this way.
Will I2P Protect Your Privacy?
In a nutshell, yes. It will protect your privacy unless you use it for regular web browsing. And even then, it would take significant resources to isolate your web traffic. I2P uses the distributed P2P model to ensure data collection, statistic gathering, and network overviews are difficult to complete. Furthermore, the garlic routing protocol encrypts multiple messages, making it much more difficult to perform traffic analysis.
The I2P tunnels we discussed earlier are uni-directional: data only flows one way. One tunnel in, one tunnel out. This alone provides greater anonymity for all peers.
I2P only encrypts data sent and received through a configured browser. Like Tor, it does not encrypt network activity for your entire system.
VPN
Finally, we have the Virtual Private Network (VPN). A VPN works differently to both Tor and I2P. Instead of focusing solely on the encryption of browser traffic, a VPN encrypts all incoming and outgoing network traffic. In that sense, it offers regular users an easy route to protecting their data, but there are some caveats that we'll explore in a moment.
How a VPN Works
Normally, when you send a request (e.g., click a link in your web browser or fire up Skype for a video call), your request pings to the server holding the specified data, and it returns to you. The data connection may be unsecured, and anyone with enough knowledge of computers can potentially access it (especially if using standard HTTP rather than HTTPS).
A VPN connects to a predefined, privately owned server (or servers), creating a direct connection called a "tunnel" (though with the rise in VPN use, this term isn't seen as frequently). The direct connection between your system and the VPN server is encrypted, as is all your data.
VPNs are accessed through a client that you'll install on your computer. The majority of VPNs use public-key cryptography. When you open the VPN client and login in with your credentials, it exchanges a public key, confirming the connection and protecting your network traffic.
Why Should You Use a VPN?
A VPN encrypts your network traffic. So everything involving an internet connection on your system is safer from prying eyes. There has been a massive surge in VPN popularity, too. They're useful for:
- Securing your data on a public Wi-Fi connection.
- Accessing region-restricted content.
- An additional layer of security when accessing sensitive information.
- Protecting your privacy from government or other invasive agencies.
Will a VPN Protect Your Privacy
Yes, a VPN will protect your privacy, but here come those caveats I alluded to earlier. Like most things, you pay for what you get. There are numerous free VPN providers, but they don't always protect you as thoroughly as you think.
For instance, many free VPN providers keep a log of all users and their internet traffic. So while encrypted data is safe coming into and out of your computer, and to and from their server, there is still a log of what you have been doing. And while the majority of VPN providers aren't about to turn you in to the authorities, they are legally obliged to turn over what they know if presented with a subpoena, and let's face it, it's you or them. No-log VPNs do exist, but you have to place heaps of trust in a service that has complete access to all incoming and outgoing data on your computer.
VPNs are an easy way to take some privacy back without having to change from your regular browser or alter your general browsing habits and internet use too much. If you're considering this option, you might also look into using a VPN kill switch.
Tor vs. I2P vs. VPN: Which Is the Best For Privacy?
If you want super-private browsing, access to onion sites and the darkweb, and don't mind a slight dip in internet speed, choose Tor.
If you want super-private access to hidden services and messaging tools across a distributed network of peers, and still don't mind a slight dip in internet speed, choose I2P (though it has fewer sites and services than Tor as a whole).
Finally, if you want to encrypt all your incoming and outgoing network traffic and really, really don't mind a slight dip in internet speed, choose a VPN.
Image Credits: ImageFlow/Shutterstock