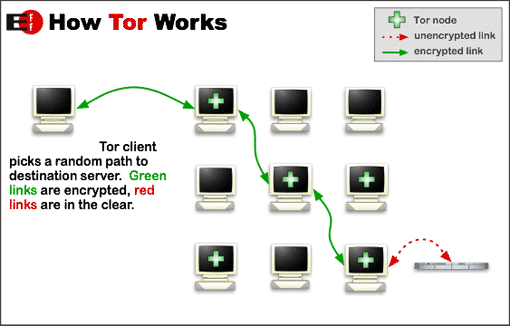
Tor has been discussed on MakeUseOf before. It's a multi-platform application that allows you to completely hide (or manipulate) the alleged origin of your network activities. It can be used to surf anonymously and also to access country-restricted services like Hulu, Spotify, and many others.
Tor reroutes network traffic through Tor nodes. With SOCKS-friendly applications like internet browsers, where we can easily specify proxies or SOCKS protocols, this isn't much of a problem. Today, I will show you how to reroute network traffic of other applications through Tor as well.
By doing this, you can hide the origin of your P2P and instant messaging applications, or even play region-restricted games online!
Redirect Application Traffic
When applications access something over the internet, it carries along your IP address, or rough point of origin. This allows other services to log your location, or even block you out. Redirecting application traffic through nodes, to cover the initial point of origin is possible - although not always as easy as with web browsers.
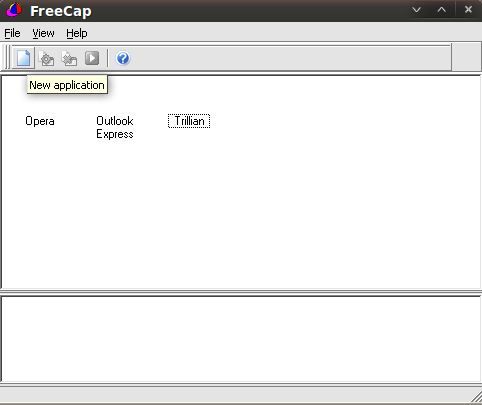
FreeCap is a free tool for Windows that does most work for you. It allows you to rerdirect the network traffic of selected applications through an HTTP or SOCKS proxy. Linux and OS X users should refer to socat.
A FreeCap alternative is SocksCap. Contrary to FreeCap, SocksCap is proprietary software and only supports SOCKS Proxies. However, it might provide a handy substitute.
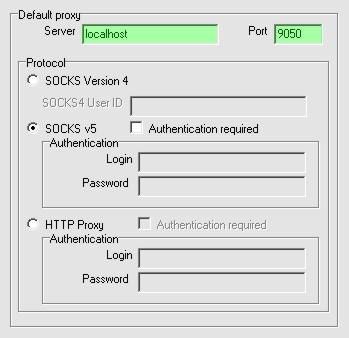
Adding applications to connect to the internet using Tor is as easy as pressing the blank paged button and specifying the program's path. Added applications will be added to the list. Make sure you have Tor's Vidalia bundle [No Longer Available] installed, and point it to localhost:9050 in File-Settings. If that doesn't work, you can try localhost:8118 as a HTTP Proxy. From then on, all network traffic from those applications will be rerouted through Tor.
Note that you can also choose to route your applications through a direct proxy. However, due to the overall slowness and inreliability of free proxies, this is far from advised.
Using A Specific Country
Like I've said before, Tor can come in real handy to access country-restricted websites. This works by masking your point of origin as though it is coming from a specific country. This can be arranged in Vidalia's configuration.
Basically, what we need to do, is to specify an exit node. This is the last link in the chain of Tor nodes, before your information reaches the destination. There used to be a moderately easy way of identifying exit nodes, this has been a problem in last versions though, so we're going to use a workaround.
Go to this page [Broken URL Removed] for a complete list of all available nodes. There are three points of interest when selecting your node: country, speed and node type. In our search, we're only going to pay attention to high-speed exit nodes (with an icon of an open door).
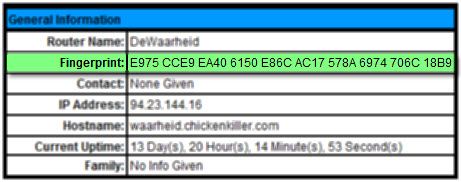
Once you've found an exit node of decent speed and from the right country, click on it to go to the node's details page.
On this page, copy the given fingerprint, eliminate all spaces and put a $ mark in front. In this particular case, we'd end up with '$E975CCE9EA406150E86CAC17578A6974706C18B9'. We're going to need this fingerprint later on.
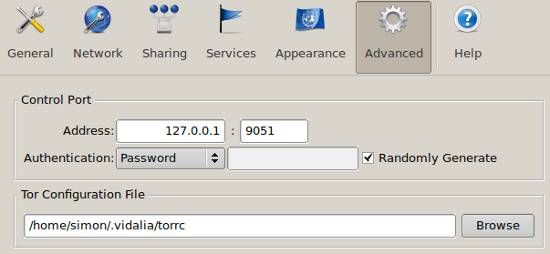
In Vidalia's Advanced settings tab, you should be able to view the path to your Tor Configuration File. This is where we're going to specify our exit nodes.
Open the configuration file with Notepad or any similar editing application. At the top of this file, paste the following two lines, with fingerprint1, fingerprint2 and fingerprint3 substituted by the fingerprint codes you wrote down before.
ExitNodes fingerprint1, fingerprint2, fingerprint3
StrictExitNodes 1
Upon restart, Tor should try to access one of those servers as an exit node. You can now access Hulu from Europe, or play games that weren't available in your region.
Do you live in a "restricted" country? Has this instructional helped you? Do you have any other solutions to bypass country-restricted websites, services or games? Let us know in the comments.