Reports that a massive leak of webmail accounts includes a huge number of credentials never seen before has been met with a mixture of panic… and doubt. How accurate is the news, and could your Gmail, Hotmail/Outlook or Yahoo Mail credentials be in the mix?
272 Million Unique Email Addresses
No, there's nothing wrong with your eyesight. It really does read "272 million". That's the total of unique pairs of email addresses and passwords obtained from a hacker by Hold Security, an information security firm who previously obtained a collection of 1.2 billion names from Russian cyber gangs in 2014. it would seem, then, that the company has good form in this area, and can be considered reliable.
But we'll come back to that.
The figure of 272 million is indeed high, and is apparently a collection of accounts from Gmail, Hotmail, Yahoo Mail and Mail.ru, a Russian and Eastern European webmail service. Hold Security claim that of the 272 million accounts, 42.5 million are new -- they've never been included in any previous data breaches.
If true, this puts the leak up there with some of the biggest of all time, such as the massive leak of 150 million Adobe user accounts and the insanely damaging Ashley Madison leak.
As with all big leaks, you can find out if your credentials are in the hands of hackers by paying a visit to www.haveibeenpwned.com. This site, featured previously on MUO, is a searchable database of data from all of the biggest hacks. If you find your credentials in there, and recognize the password as a current one, it's time to change it. Meanwhile, if the account is now unused, it's worth closing it.
Now, what about these 42 million accounts?
Who Leaked the Data?
The story behind this leak seems shrouded in mystery. Hold Security's blog post on the matter suggests that they were contacted anonymously with over 900 million credentials collected from multiple breaches over a period of time, a 10 gigabyte file in total.
We don't know the person who leaked the data, other than he is described as "this kid from a small town in Russia" and that he was paid in social media likes. No, really.
How Data Breaches Can Be Used by Hackers
So what does it mean, really? How can anyone make use of 10 gigabytes worth of leaked email credentials? Well, give it some thought: how many websites do you log into with your email account?
Speaking to the BBC, Milwaukee-based Hold Security's chief information security officer, Alex Holden, explained how "there are hacker sites that advertise 'brute forcing' popular services and store fronts by taking a large amount of credentials and running them one-by-one against the site."
One by one, password after password is being attempted on services like Amazon, eBay, perhaps Xbox Live and PlayStation Network, using the brute force technique, demonstrated here:
Worse still, the credentials have probably been shared around the world by now, Holden admits:
"What makes this discovery more significant is the hacker's willingness to share these credentials virtually for free, increasing the number of... malicious people who might have this information."
But security breaches can also be used by security companies. Back in 2014, Hold Security attempted to cash in on the breach it reported that time around, offering a subscription service to website owners (but not individuals). Some researchers claim that their previous moment in the spotlight was a case of style over substance, but Holden denied this was the case, claiming to be "actually losing money. We’re not trying to do it for publicity at all from the perspective of profiting, we are not pushing our services. In fact, we’re trying not to go broke."
Whether you believe Holden isn’t the point, however. The point is that the leak includes data that could be yours. What can you do about it?
I Should Change My Password, Right?
If you're the owner of a Hotmail, Outlook, Gmail, Yahoo Mail or Mail.ru account, you're probably thinking that right about now is the best time to change your account password. Well, for a moment, hold your horses. Renowned security researcher Professor Alan Woodward told the BBC that "there was 'no need to panic' or for people to change their passwords at this point."
Now, we're not saying that you shouldn't change your password; you're free to do so at any time, as it is your account. However, if the breach is as serious as it is being claimed, your webmail provider will be requiring you to change your password the next time you attempt to login.
Prof. Woodward is being quite canny here, advising users to wait for instructions from their webmail provider. Why? Well, for a start off, it's Gmail, Hotmail/Outlook, Yahoo Mail and Mail.ru who have the resources to investigate the legitimacy of the breach, and it is those companies who have the power to initiate mass password resets.
Additionally, webmail providers have tools in place to detect suspicious logins. All in all, they have the situation under control.
The Threat of Phishing and Spam
A big problem with high profile security breaches is that they bring with them additional threats. Like pilot fish, criminals are never far from the big payout, ready to collect the scraps that are cast aside. There is a big threat from phishing following this particular piece of news.
First of all, if you use Gmail, Hotmail or Outlook, Yahoo Mail, or Mail.ru, you may notice an increase in spam email messages. Some may come from new sources, and be difficult for your webmail provider to deal with in the usual way (that is, keep it in the spam/junk folder, out of your sight). As a result, extra vigilance is necessary.
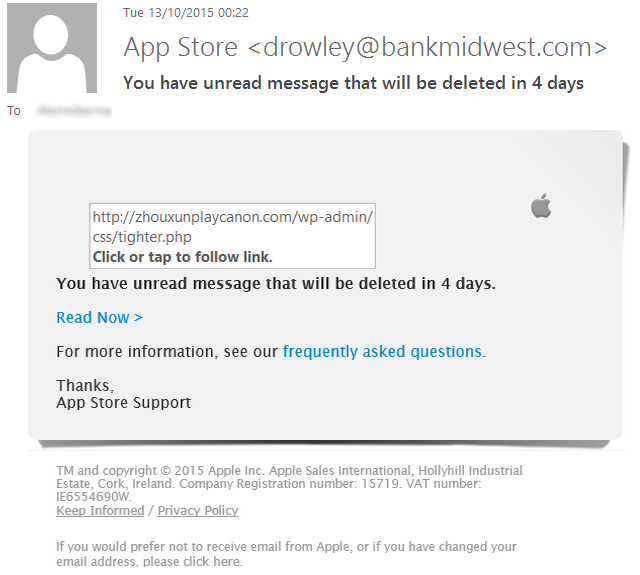
Perhaps most importantly, you need to be aware of the likelihood of phishing emails claiming to be from the webmail provider, asking you to click a link to reset your password. The link, of course, will be to a spoofed website, ready to collect your current credentials.
None of the webmail providers concerned are likely to send you an email of this type.
Stay Secure, and Avoid Phishing Emails
We seem to be living in a golden age of security breaches (for the hackers, at least), and it shows no sign of letting up. As long as there are online systems, and a profit to be made, there will be people with the skills and motivation to breach those systems.
Combating this requires better vigilance from the businesses and services we share our email addresses and personal details with; it also need us to be alert to the threats, and how they might be executed. Spam emails, phishing, spoof websites – they're all likely attack vectors heading for your inbox.
How do you feel about this latest security breach? Are you becoming tired of hearing about online leaks that could be avoidable with tighter security in place? Tell us what you think – start the conversation in the comments box.
Image Credits: stealing a purse by Volkova Vera via Shutterstock, Brian Senic via Shutterstock.com, JMiks via Shutterstock.com