The FBI's controversial Next Generation Identification (NGI) system has been making headlines recently after a request to exempt it from the Privacy Act. But what, exactly, is in the database? Why should we worry if it's exempted? And should you be concerned about it violating your privacy? Here's what you should know about the NGI and how it relates to the Privacy Act.
What Is the Next Generation Identification System?
Most of the time when we talk about surveillance and privacy worries, we're talking about the NSA. But the FBI has been playing an increasingly large role in discussions over privacy and security as well, like when it tried to compel companies to put backdoors into their products that would compromise users' security.
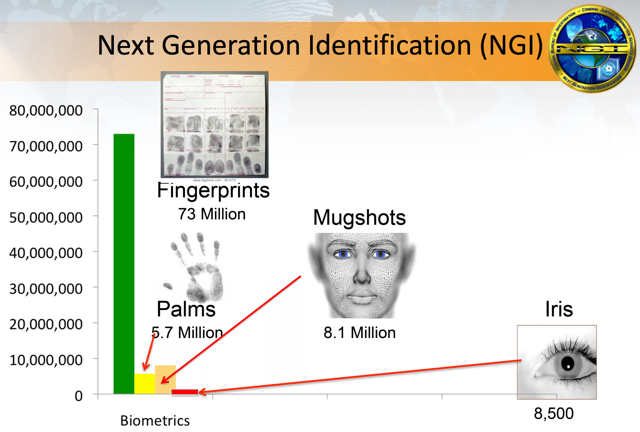
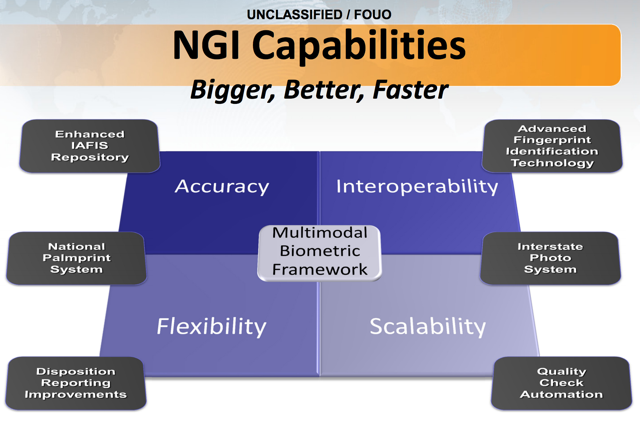
According to the FBI's website, the NGI "provides the criminal justice community with the world’s largest and most efficient electronic repository of biometric and criminal history information." The page describing the system lists fingerprints (including latent prints and palm prints), a facial recognition system, and iris scans as parts of the database. It also provides other services, including an automatically updating background check service, a cold-case search system, and a repository of "individuals of special concern."
Other sources speculate on additional pieces of information that could be stored, including DNA profiles, gait analyses, photos of tattoos, voice recordings, and other valuable identifying data. Whether these are in the database or how widely they're used isn't immediately clear, but the FBI does call the NGI the "world’s largest and most efficient electronic repository of biometric and criminal history information," so it does seem likely that they're storing as much as they possibly can.
Because the FBI is trying to create the world's largest database of this type of information, they're using as many sources of information as possible, which is another point of contention, as it's not just criminals whose information is stored.
Information from background checks (the majority of which are probably run on non-criminals) is also stored there, as well as information on people applying for permanent residency or naturalization. And with the number of spurious arrests that don't result in convictions, another source of non-criminal information is flowing directly into the NGI.
The Problems with the NGI
Okay, so we have another national database of identifying information for use by law enforcement: what's the big deal? We've had a giant database of fingerprints maintained by the FBI for many years, and the addition of new information was bound to happen, right? While that might be true, there are some specific, worrying things about the NGI, that have a lot of people clamoring for a change.
First, it contains non-criminals' information. That's a pretty big deal, and a lot of people think that violates our rights to privacy. The storage of identifying information in a national law enforcement database is worrying on a number of levels, and has a very dystopian, surveillance-state feel to it. Do you think you should be in an FBI database if you've never been arrested, much less convicted?
Second, it may not affect everyone equally. A recent letter to the FBI (pdf) signed by a large number of organizations, including the ACLU, the Constitutional Alliance, the Electronic Frontier Foundation, the National LGBTQ Task Force, and a range of others, pointed out that a number of factors may result in this information affecting people very differently. For example, the database likely contains a disproportionate amount of African-Americans, Latinos, and immigrants.
In addition to legal and ethical challenges, this fact also poses a technical one. The aforementioned letter pointed out that research, including research authored by the FBI, indicates that "some of the biometrics at the core of NGI, like facial recognition, may misidentify African Americans, young people, and women at higher rates than whites, older people, and men, respectively."
Third, information in the database may not be complete. Arrest records, for example, are often missing information on whether a person was convicted, acquitted, or had their charges dropped. A recent investigation reported that potentially thousands of people have lost work due to incomplete or incorrect FBI background check records. Expanding the amount of information in the database isn't likely to help that problem.
Fourth, too much data makes it harder to find relevant, important information. A number of whistleblowers and officials have come forward saying that both the US and UK surveillance systems are so overwhelmed with the huge amount of information they collect that they're becoming inefficient in actually finding useful data. One NSA official has even stated that this has led to successful terrorist attacks, and a similar report has come out of the UK.
Collecting and storing a huge amount of information on criminals and non-criminals, especially when that data is incomplete, is a danger to both to law enforcement and citizens.
What You Should Be Most Worried About
As if the points listed above weren't bad enough, the FBI has made a request for legislation that would exempt the NGI from the Privacy Act, a very important piece of legislation that seeks to increase transparency in government actions so citizens can ensure accountability. A number of important provisions are included in the act, and the FBI wants the NGI to be exempt from all of them. This would have a number of repercussions.
Citizens would no longer have the right to get information about their records. The Privacy Act states that anyone can request their record from a government database so it can be reviewed and any errors corrected. That right would be eliminated if the database were exempted, meaning no one would ever know what information the FBI had on them.
The FBI could collect any information it wanted. According to the letter referenced earlier, "the Privacy Act generally bars the government from creating databases about the political activities of its citizens . . . Under the FBI’s proposal, the FBI could violate that rule – and private citizens could never take them to court." With no way to find out what information is in any individual's file, there's no accountability, and the FBI could collect any data they choose, regardless of whether it's legal or not.
Records could be shared among any individuals and agencies. The Privacy Act states that the subject of any given record must be notified that an agency wishes to share their information with any other person or agency, and that the person who the record pertains to must give their permission for the transfer. Without that clause, government agencies and individuals could share any information they want.
There are already exceptions in place for this rule, including an exception for law enforcement, but a mass exception to this provision is worrying.
The FBI already has a long record of trying to keep this database and its affect on privacy a secret:
For years, the American public has waited for the FBI to publish basic privacy notices about this database. Federal law requires that the FBI publish a System of Records Notice (SORN) and/or a Privacy Impact Assessment (PIA) when the agency starts to keep – or significantly changes – a database like NGI. For years, the FBI has not met these requirements.
Despite significant specific requests, the NGI has remained in the shadows.
In 2011, for example, the FBI began to allow state law enforcement to run facial recognition searches against photos in the NGI database. Despite pressure from Congress and civil society, the FBI didn’t release a Privacy Impact Assessment about this program until September 2015. In fact, even though NGI itself was launched in 2008, the FBI didn’t publish a System of Records Notice about NGI until May 5, 2016 – the same day it proposed to exempt the system from other, even more basic transparency requirements.
Of course, there are some good reasons for exempting parts of the database from some parts of the Privacy Act. Especially when it comes to law enforcement; full transparency isn't feasible or even always a good idea. But the FBI isn't asking for specific exemptions: they're asking for a full exemption for the entire database from the entire Privacy Act.
The FBI has also repeatedly changed its story on what will be included in the NGI, and some of its plans contradict earlier statements and, potentially, privacy laws. For example, the EFF reported that the FBI was working on a way for law enforcement officers to collect biometric data in the field and submit it directly to the NGI, which explicitly contradicts what they told Congress in 2012 about only using mugshots.
A number of other contradictory and worrying statements about this database, have also been made, and exempting it from the Privacy Act will turn it into a black hole of citizen surveillance.
A Worrying Development
As of right now, we don't know if the NGI will be exempted from the Privacy Act. Although there is public pressure to keep privacy protections intact, the words "national security" and "terrorism" often convince members of Congress and the judiciary that privacy should be compromised for increased security, despite the fact that increased surveillance often results in decreased efficacy.
If you feel strongly about keeping privacy protections in place on the FBI's biometric database, now is the time to act, as a decision on its Privacy Act exemption is likely coming soon. A number of petitions are available for you to sign (check out this one from Color of Change), and getting in touch with your Congressional representatives is always a good idea when it comes to issues this big.
What do you think of the FBI's biometric database? Are you worried about privacy violations, or are you willing to sacrifice some protections for an attempt at increasing national security? Share your thoughts in the comments below!
Image credits: State of California Office of the Attorney General [No Longer Available].