So you didn't care about Google, Amazon, Facebook, and Samsung eavesdropping on you. But how do you feel about cyber criminals listening in on your bedroom conversations? WikiLeaks's Vault 7 file suggests you may soon play host to unexpected visitors.
The Central Intelligence Agency's most dangerous malware -- capable of hacking nearly all wireless consumer electronics -- could now sit in the hands of thieves and terrorists. So what does that mean for you?
What's Vault 7?
Vault 7 is a leaked trove of documents pertaining to the Central Intelligence Agency's (CIA) cyber warfare capabilities. Much of the software described in Vault 7 reveals how the CIA controls and surveils using smartphones, tablets, smart TVs, and other internet-connected devices. On March 7th, WikiLeaks published a tiny fraction of the documents.
What should terrify everyone: According to WikiLeaks, the CIA lost control of these tools. And now criminals (probably) possess them. However, many of the published exploits (there are many as-of-yet unpublished exploits) are almost five years old and have since been patched.
How Criminals Obtain U.S. Hacking Tools
Not everyone who works for an intelligence agency is a card-carrying member. The CIA regularly outsources employment to federal contractors in the private sector. Many of these private intelligence firms, such as HBGary, lack the CIA's security.
Edward Snowden Was a Federal Contractor
For example, Booz Allen Hamilton employed NSA contractor Edward Snowden, who famously leaked documents pertaining to the NSA's illegal surveillance programs. Additionally, Booz Allen Hamilton suffered a 2011 hack.
In its official statement, WikiLeaks asserted (emphasis mine):
The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
One part of the quote stands out: the tools were circulated in an "unauthorized manner". The implication should concern everyone in the world. The CIA probably lost control of a $100 billion portfolio of hacking tools.
But this isn't the first time that private actors acquired dangerous, government-developed software.
The Stuxnet Worm
For example, the Stuxnet worm, another weaponized malware, fell into the hands of cyber criminals soon after its 2010 discovery. Since then, Stuxnet occasionally pops up as malware. Part of its ubiquity relates to its codebase. According to Sean McGurk, a cyber security researcher, the source code for Stuxnet is available for download.
You can download the actual source code of Stuxnet now and you can repurpose it and repackage it and then, you know, point it back towards wherever it came from.
That means pretty much any coder can build their own Stuxnet-based malware kit. The CIA's lack of control over its cyber arsenal ensures that exploits will continue flowing into the hands of for-profit criminals, terrorists, and rogue states. No better example exists than the ShadowBrokers.
The Shadow Brokers
In 2016, the Shadow Brokers group infamously auctioned off a series of state-manufactured hacking tools. How they stole the tools is anyone's guess, but where they acquired them is known: the NSA.
According to The Intercept, documents inside the Snowden leak connect the tools stolen by the Shadow Brokers with the hacking group known as Equation Group (EG). EG employed exploits that were later found in the state-sponsored Stuxnet worm -- which highly suggests a connection between the NSA and EG. Combined with the leaked tools, it appears that the NSA and CIA are unable to control their own technologies.
But does that mean your privacy and security are compromised?
A History of Spying on Customers
Your privacy and security are already compromised.
Almost all modern smart products include microphones. Some devices require pressing a button to turn on the microphone or camera. Others listen continuously for the utterance of a keyword. For example, Samsung's range of smart TVs constantly listen, record, and transmit -- all without relying on sophisticated government surveillance.
Smart TVs Are Owned
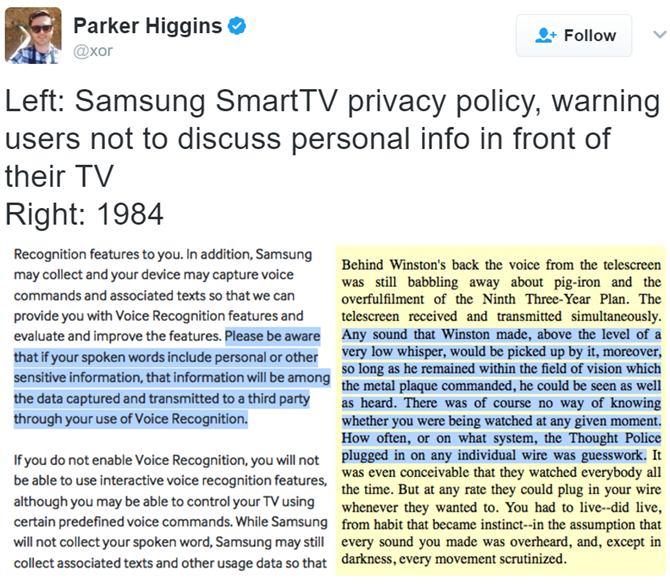
Samsung's privacy statement regarding their smart TVs is troubling. Although Samsung modified their privacy terms-of-service to avoid controversy, the original statement, captured by Twitter user xor, goes as follows:
Here's the relevant quote from Samsung (emphasis mine):
Please be aware that if your spoken words include personal or other sensitive information, that information will be among the data captured and transmitted to a third party through your use of Voice Recognition.
In short, smart televisions hear everything you say. And Samsung shares that data with third parties. Those third parties, however, are assumed to be businesses with only a commercial interest in your conversations. And you can always turn the thing off.
Unfortunately, the "Weeping Angel" hack developed by the CIA makes it so the TV can't turn off. Weeping Angel targets Samsung smart TVs. The Vault 7 documentation refers to this as Fake-Off mode. From WikiLeaks:
...Weeping Angel places the target TV in a "Fake-Off" mode, so that the owner falsely believes the TV is off when it is on. In "Fake-Off" mode the TV operates as a bug, recording conversations in the room and sending them over the internet to a covert CIA server.
Samsung isn't alone. After all, Facebook, Google, and Amazon (our review of the Echo) also rely on using the microphones of devices -- often without the knowing consent of users. For example, Facebook's privacy statement claims that they do use the microphone, but only when the user uses "specific" features of the Facebook application.
How Technology Enables Illegal Surveillance
The biggest security flaw on modern smartphones is its software. By exploiting security vulnerabilities in a browser or operating system, an attacker can remotely access all features of a smart device -- including its microphone. In fact, that's how the CIA accesses most of its targets' smartphones: right over a cellular or Wi-Fi network.
Of the 24 Android exploits developed by the CIA, its contractors, and cooperating foreign agencies, eight can be used to remotely control a smartphone. I assume that once under control, the malware operator would then use a combination of attacks, combining remote access, privilege escalation, and the installation of persistent malware (as opposed to malware that lives in RAM).
The techniques listed above normally rely on the user clicking a link in their email. Once the target navigates to an infected website, the attacker then can take control of the smartphone.
A False Hope: The Hacks Are Old
On a false note of hope: of the hacks revealed in Vault 7, most pertain to older devices. However, the files only include a fraction of the total hacks available to the CIA. More than likely, these hacks are mostly older, obsolete techniques, which the CIA no longer uses. However, that's a false hope.
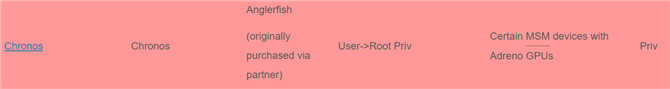
Many of the exploits apply broadly to systems-on-a-chip (what's an SoC?) rather than to individual phones.
For example, in the graphic above, the Chronos exploit (among others) can hack the Adreno chipset. The security flaw encompasses almost all smartphones based on Qualcomm processors. Again, keep in mind that less than 1 percent of Vault 7's content has been released. There are likely many more devices vulnerable to penetration.
However, Julian Assange offered to help all major corporations patch the security holes revealed by Vault 7. With any luck, Assange might share the archive with the likes of Microsoft, Google, Samsung, and other companies.
What Vault 7 Means for You
The word isn't in yet on who possesses access to the archive. We don't even know whether or not the vulnerabilities still exist. However, we do know a few things.
Only 1 Percent of the Archive Has Been Published
While Google announced it fixed most of the security vulnerabilities used by the CIA, less than 1 percent of the Vault 7 files have been released. Because only older exploits were published, it's likely that almost all devices are vulnerable.
The Exploits Are Targeted
The exploits are mostly targeted. That means that an actor (such as the CIA) must specifically target an individual in order to gain control of a smart device. Nothing in the Vault 7 files suggests that the government is sweeping up, en masse, conversations gleaned from smart devices.
Intelligence Agencies Hoard Vulnerabilities
Intelligence agencies hoard vulnerabilities and do not disclose such security breaches to corporations. Because of shoddy operations security, many of these exploits eventually make their way into the hands of cyber criminals, if they are not already there.
So Can You Do Anything?
The worst aspect of the Vault 7 revelations is that no software provides protection. In the past, privacy advocates (including Snowden) recommended using encrypted messaging platforms, such as Signal, in order to prevent man-in-the-middle attacks.
However, Vault 7's archives suggest that an attacker can log a phone's keystrokes. Now it seems that no internet-connected device avoids illegal surveillance. Fortunately, it's possible to modify a phone to prevent its use as a remote bug.
Edward Snowden explains how to physically disable the camera and microphone on board a modern smartphone:
Depending on the model of phone, Snowden's method requires physically desoldering the microphone array (noise canceling devices use at least two microphones) and unplugging both the front-facing and rear-facing cameras. You then use an external microphone, instead of the integrated mics.
I'd note, though, that unplugging the cameras isn't necessary. The privacy-minded can simply black out the cameras with tape.
Downloading the Archive
Those interested in learning more can download the entirety of the Vault 7 dump. WikiLeaks intends on releasing the archive in small chunks throughout 2017. I suspect that the subtitle of the Vault 7: Year Zero refers to the enormity of the archive's size. They have enough content to release a new dump every year.
You can download the complete password protected torrent. The password for the first part of the archive is as follows:
Are YOU concerned about the CIA's loss of control over their hacking tools? Let us know in the comments.
Image Credit: hasan eroglu via Shutterstock.com