About Guy McDowell
With 20+ years of experience in IT, training, and technical trades, it is my desire to share what I've learned with anyone else willing to learn. I strive to do the best job possible in the best manner possible, and with a little humour.
Latest Articles

Free Military-Grade Privacy For Your Files: How Bitlocker Works [Windows]
Ever heard that quote about trying to explain how a television works to an ant? I'm not calling you an ant, even though you are hard-working and enjoy the occasional sip of aphid milk. What I am saying is that I'm going to explain how Windows BitLocker works, without you having to have a degree in computer science and cryptography experience.
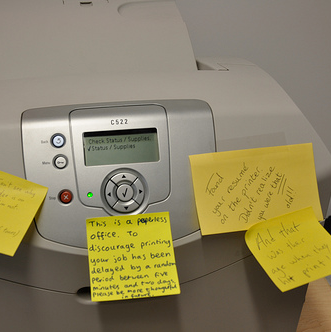
How To Pick The Best Printer For Your Budget & Workload
So much for the paperless office! The integration of information technology has seemingly increased the amount of paper printing we have to do. So pretty much everyone with a computer needs a printer at some point in time. The problem is figuring out which printer is the best one for your budget AND workload. Laser, colour, inkjet, large format, photo quality, all-in-one, WiFi enabled, monochrome...there are a lot of jargon words around printers.

Don't Let Them Scan You: Blocking RFID Chips
Every convenience in life comes at a cost. That's why things are so expensive at the corner store compared to the grocery store. They aren't selling you a carton of milk, they're selling you a way out of a mistake in not remembering to pick up your milk early at the supermarket. That kind of convenience has a readily tangible cost - more money out of your wallet. The convenience cost of other things, such as technology, might not be so readily apparent.

Use the Right Battery Type for the Job
Batteries are batteries right? Sure, and computers are computers, and tires are tires. Oh, what's that? You say there's a big difference between a Mac and PC, and tractor tires and car tires? Well, so too there are big differences between the different types of batteries that are available. Obviously the physical sizes are different like your AAA's and your D's, but the differences go deeper. The construction and composition of the charge generating materials can be significantly different as well.

Gamer Droid: Video Game Themed Wallpapers For Android
I love video games! You love video games! The difference between you and I is that you probably actually play with them while I admire them from afar. Fact is, I'm still playing Icewind Dale. But that's not the point. The point is I can still enjoy the presence of my favourite video games in new and exciting ways on my Samsung Android phone. And you can too! When I first went looking for video game wallpapers for my phone, I was vaguely aware of what a Live Wallpaper was.

Virtual HAM Radio - No License, No Gear, All Fun
HAM radio. If you even know what it is, it conjures up images of grown men hiding in dark places with glowing vacuum tubes and devices with knobs and twiddle-bits. They're talking across the world about who knows what. They're part electronics guru, part mad scientist, part excited kid. These are the guys that preceded the computer gurus of today. These are the guys that could reach across the world when no one else could.

8 Amazing iPad Mods and Hacks
Are you content leaving all the cool design to Apple to do for your iPad? Or do you want to push it a bit further yourself? Maybe you saw what someone did with a PC case once and thought, "I wish I could do that to my iPad." You can. It's yours, do what you like with it. Just don't expect to have any warranty coverage once you do.

10 Ways Your Smartphone Camera Can Make Life Easier
"Does your phone have a camera on it?" said no one since 2005. Nobody even asks how many megapixels your phone's camera has anymore. With the ubiquity of smartphones today, and the resolution of the cameras they have in them, why does anyone even sell a point-and-shoot digital camera anymore? All you need is a decent smartphone to take your vacation pictures and click a button to upload them to Facebook, Pinterest, Tumblr, wherever.
DNS Is Just A Proxy - Use A VPN To Access Region Blocked Video
For copyright reasons, certain media companies only allow their content to be viewed in certain geographic areas. In plain English, what this means is that they are meanies who suck. And what does the Internet do to meanies who suck? We find workarounds. Before I get to the tools, I’d like to talk about the process of geographical Internet Protocol (IP) address blocking and circumventing those blocks.

Understanding Your Internet Speed
So you're paying for a certain internet speed but what does that speed actually mean? How fast is it? And why does it seem so slow at times?

How Does StumbleUpon Work? [Technology Explained]
StumbleUpon is one of the most interesting sites on the web. Here's how the stumbling algorithm works and how it chooses which sites to show you.